Configure Azure Key Vault connection¶
The following guide illustrates connecting Certificate Manager - SaaS with Azure Key Vault (AKV).
Enable Certificate Manager - SaaS to provision new certificates in Azure Key Vault (AKV) for use with Azure services. Also, now users have the capability to import existing certificates into keystores. This enables tasks such as rotating, renewing expiring certificates, auto-renewal, changing certificate authorities (CAs), and more.
This guide walks you through the integration process.
Before you begin¶
You're going to need a few things to complete this procedure.
- You will need an Azure account.
- Your Azure Application (client) ID.
- Your Azure (tenant) ID.
- Your Azure Client secret.
- You will need at least one active VSatellite to provision certificates to Azure.
- Venafi permissions for Azure: You must specify these permissions when defining the role's permission policy.
- To enable specific services to access Key Vault via the Key Vault Firewall, add Venafi's IP address to the Key Vault firewall's allowlist. You can find the required IP address in the Allowlist public NAT gateways topic.
Note
- Only Certificate Manager - SaaS-generated and user-imported certificates with private keys can be provisioned. To learn more see Importing a private key via API (PKCS #8) and Importing a private key via API (PKCS #12).
- Only one certificate can be provisioned at a time.
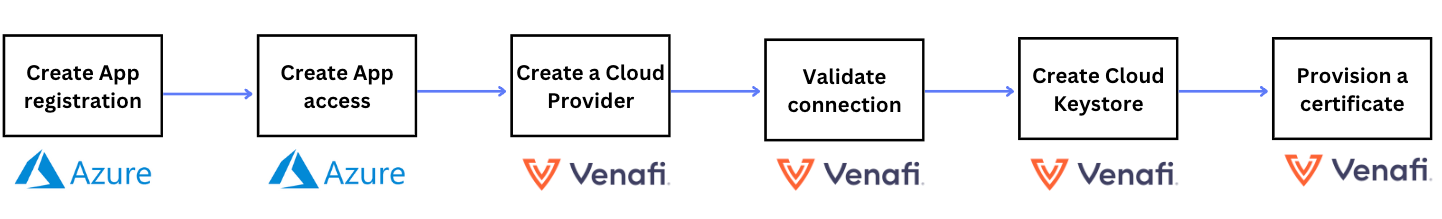
Overview¶
The following diagram illustrates the high-level steps for integrating Certificate Manager - SaaS with Azure Key Vault (AKV). In the subsequent sections, we dive into each of these steps, providing you with a guided walkthrough.
Step 1: Create an Azure App registration (Service Principal)¶
- Log in to the Azure Portal.
- In the left panel, select Microsoft Entra ID and then App registrations.
- Select the New Registration button in the top left corner.
- In the Register an application panel, enter the following values:
- Name - Enter a name that carries significance and can be readily linked to this specific cloud provider.
- Supported account types - Choose the appropriate supported account types.
- Redirect URL - Leave this blank or enter a redirect URI if needed.
-
Select Register.
Important
You will be presented with your app registration details. Make sure to copy and save the Application (Client) ID and Azure (Tenant) ID for later use.
-
Select the Add a certificate or secret, and then New client secret. Enter a description and click Add. You will be presented with your Secret ID only once, make sure to copy and save it for later use.
Step 2: Create Application access in Azure¶
In this step we grant permissions on Key Vault resources for the app (Service Principal) you just registered.
Tip
You will need to add the following permissions to your app to manage Azure Key Vault resources.
- List subscriptions
- List key vaults
- List certificates
- Import certificate
- Get certificate
There are 3 ways to add these permissions:
- Add built-in Azure RBAC role(s) to appropriate resources (e.g., a Resource Group or a Key Vault).
- This option is the quickest, but built-in roles are not as granular.
- Use this option if ease of implementation is your priority. We select the minimum number of built-in roles to allow access by Certificate Manager - SaaS.
- Add a custom Azure RBAC role to appropriate resources (e.g., a Resource Group or a Subscription).
- This option requires extra steps, but custom roles are sufficiently granular only to give minimum required access.
- Use this option if most granular and minimal access is your priority and you do not mind adding a custom role to Resource Groups or Subscriptions.
- Add Azure Access Policy configuration to appropriate Key Vault resources.
- This option is semi-granular, meaning that the access policy is granular, but a single "reader" built-in Azure RBAC role is also required.
- Use this option only if you prefer to use Azure Access Policy. This option does not have advantages over a custom RBAC role but has some disadvantages (such as configuring each Key Vault).
Granting Permissions with Azure Role-Based Access Control (RBAC) Permissions Model¶
Using Built-In Role(s)¶
Tip
If you are managing your Key Vaults via a Resource Group, then you can add the roles below to said Resource Group, which will be inherited by all contained Key Vaults.
- Select applicable Key Vault (or Resource Group if managing Key Vaults via a Resource Group).
- Select Access control (IAM).
- Select + Add and then Add role assignment.
- Select Job function roles unless already selected.
- In the search bar enter Key Vault Certificates Officer, this will produce a list, highlight Key Vault Certificates Officer and select Next.
- Click + Select members, this will open a panel to your right. Enter the app name you registered in Step 1 and select that app.
- Select Review and assign.
Repeat for each Key Vault (or Resource Group) you wish to configure for access by Certificate Manager - SaaS. Your app (registered in Step 1) should have the following role on applicable Key Vaults:
- Key Vault Certificates Officer
Using Custom Role¶
Create Custom Role¶
Note
This role can only be configured on a Resource Group or a Subscription. If you manage your Key Vaults via Resource Groups, you can add this role to appropriate Resource Groups. Otherwise, add this role to appropriate Subscriptions.
Role names are unique and you'll have to use a different name for each custom role you'll need to create.
- Select the applicable Subscription (or Resource Group if managing Key Vaults via a Resource Group) that contains the Key Vaults you wish to give access to.
- Select Access control (IAM).
- Select + Add and then Add custom role.
- Select the JSON tab and then click the Edit button.
- Give your role a (unique) name and (optional) description by filling in the appropriate JSON fields (roleName and description).
- For the permissions element, replace it with the following:
"permissions": [ { "actions": [ "Microsoft.KeyVault/vaults/read", "Microsoft.KeyVault/vaults/secrets/read" ], "notActions": [], "dataActions": [ "Microsoft.KeyVault/vaults/certificates/read", "Microsoft.KeyVault/vaults/certificates/update/action", "Microsoft.KeyVault/vaults/certificates/create/action", "Microsoft.KeyVault/vaults/certificates/import/action" ], "notDataActions": [] } ] - Click the Save button.
- Select Review + Create, and then select Create.
You'll have to repeat the above for each Subscription or Resource Group containing Key Vaults you wish to give access to.
Assign Custom Role¶
- Select the applicable Key Vault (or Resource Group if managing Key Vaults via a Resource Group).
- Select Access control (IAM).
- Select + Add and then Add role assignment.
- Select Job function roles unless already selected.
- In the search bar, enter your custom role name. This will produce a list, highlight your custom role, and select Next.
- Click + Select members. This will open a panel to your right. Enter the app name you registered in Step 1 and select that app.
- Select Review and assign.
Repeat this for each Key Vault (or Resource Group) you wish to configure for access by Certificate Manager - SaaS. Your app (registered in Step 1) should have your custom role on applicable Key Vaults.
Granting Permissions with Vault Access Policy Permissions Model¶
Note
You can still use the RBAC permissions model with these Key Vaults, so if you wish to use the above RBAC configuration, use the instructions in the previous section, and they will apply to these Key Vaults as well.
First, we need to grant one Azure RBAC permission:
Tip
If you are managing your Key Vaults via a Resource Group, then you can add the roles below to said Resource Group, which will be inherited by all contained Key Vaults.
- Select applicable Key Vault (or Resource Group if managing Key Vaults via a Resource Group).
- Select Access control (IAM).
- Select + Add and then Add role assignment.
- Select Job function roles unless already selected.
- In the search bar enter Key Vault Reader, this will produce a list, highlight Key Vault Reader and select Next.
- Click + Select members, this will open a panel to your right. Enter the app name you registered in step 1 and select that app.
- Select Review and assign.
Repeat for each Key Vault (or Resource Group) you wish to configure for access by Certificate Manager - SaaS. Your app (registered in Step 1) should have the following role on applicable Key Vaults:
- Key Vault Reader
Now we can grant access policy permissions:
These permissions must be granted on each Key Vault you wish to manage. They cannot be granted via a Resource Group.
- Select applicable Key Vault.
- Select Access policies.
- Select + Create.
- Under Secret permissions, select Get.
- Under Certificate permissions, select Get, List, Update, Create, Import.
- Select Next.
- For principal, enter the app name you registered in Step 1 and select that app.
- Select Next, then select Next again.
- Select Create.
Repeat for each Key Vault you wish to configure for access by Certificate Manager - SaaS.
Step 3: Create a Cloud Provider¶
- Sign in to Certificate Manager - SaaS.
- Click Integrations > Cloud Providers.
- Click New and select Azure.
- Enter a Name for the new cloud provider. This name will help Certificate Manager - SaaS users to identify this cloud provider.
- Select an Owning Team. If you need to create a new team see, create a new team.
-
Click Continue.
Note
- Owning Team - The Owning Team is responsible for the administration, management, and control of a designated cloud provider, with the authority to update, modify, and delete cloud provider resources.
- Authorized Team - The Authorize Team is granted permission to use specific resources of a cloud provider. Although team members can perform tasks like creating a keystore, their permissions may be limited regarding broader modifications to the provider's configuration. Unlike the Owning Team, users may not have the authority to update and delete Cloud Providers.
-
Enter your Application (client) ID, Directory (tenant) ID, and Client secret obtained from Azure in the above steps.
Info
- Azure Application (client) ID - is an Active Directory Application Id. The client Id is the unique identifier of an application created in Active Directory. You can have many applications in an Active Directory and each application will have a different access levels.
- Azure (tenant) ID - is the unique identifier of the Azure Active Directory instance. One subscription can have multiple tenants. Using this Tenant Id you register and manage your apps.
- Azure Client secret - is a credential that is used to authenticate and authorize a client application when it interacts with Azure services.
-
Click Save. At this point, your new provider details will be displayed in the right pane.
Step 4: Validate the connection¶
In this step we will validate the connection between Certificate Manager - SaaS and Azure.
- Click Integrations > Cloud Providers.
-
Find the new cloud provider we created in Step 1. Click the more options
 button to the right and select Test Access.
button to the right and select Test Access.
If you still have the yellow icon ![]() next to your cloud provider, this means you were not able to successfully validate your connection. Go back and check your settings in the above steps.
next to your cloud provider, this means you were not able to successfully validate your connection. Go back and check your settings in the above steps.
Step 5: Add a Cloud Keystore¶
- Sign in to Certificate Manager - SaaS.
- Click Installations > Cloud Keystores.
- Click New and select Azure.
- Enter a Name for the new cloud keystore.
- Select an Owning Team. If you need to create a new team, see create a new team.
-
Select an Authorized Team.
Note
- Owning Team - The Owning Team is responsible for the administration, management, and control of a designated cloud provider, with the authority to update, modify, and delete cloud provider resources.
- Authorized Team - The Authorize Team is granted permission to use specific resources of a cloud provider. Although team members can perform tasks like creating a keystore, their permissions may be limited regarding broader modifications to the provider's configuration. Unlike the Owning Team, users may not have the authority to update and delete Cloud Providers.
-
Select an Azure Cloud Provider.
- Select a Subscription Name.
- Select an Azure Key Vault Name.
- (Optional) To begin discovery once the keystore is created, an option to discover certificates on your keystore, select the toggle switches to turn on
 "Start discovery immediately" and "Include expired certificates". After creating the keystore, refer to Set up AKV Discovery Schedule to create your schedule.
"Start discovery immediately" and "Include expired certificates". After creating the keystore, refer to Set up AKV Discovery Schedule to create your schedule. - Click Save. At this point you should see your saved new cloud keystore in the Cloud Keystore list.
- (Optional) If you didn't start discovery when creating the keystore in the above step, click the Discover Now button. You will notice a message in the top right of the pane indicating "Discovery Status: Running". Your results will begin to populate in the same pane.
Step 6: Provision a certificate¶
At this point you should now have the ability to provision certificates.
-
Click the
 button to the right of the new cloud keystore you just created and select Provision.
button to the right of the new cloud keystore you just created and select Provision.Tip
Here you also have the option to delete certificates if needed.
-
From the dropdown, search for the certificate you want, select it, and click Provision. This creates a new certificate (new installation on the keystore).
-
(Optional) Here, you also can re-provision, replace, or delete a certificate. These options modify an existing machine installation.
- Select your Cloud Keystore, and a details panel will appear on the right.
- Click on the
 button to the right of your certificate.
button to the right of your certificate. - Choose the appropriate action: Re-provision, Replace, or Delete, and proceed through the user interface steps until the process is complete.
Info
- Re-provision - This action re-provisions your current certificate.
- Replace - Choose this option to substitute your current certificate with a different one.
- Delete - This action removes the selected certificate from the table.
Note
If using Google Cloud Platform, go to your Google service account, under Certificate Manager, and select Certificates. Click the Refresh button. You should now see your certificate in the list with an active status.
At this point you have successfully connected Certificate Manager - SaaS to your cloud provider and successfully provisioned a certificate.
Set up AKV Discovery Schedule¶
- In the Certificate Manager - SaaS toolbar, click Installations and select Cloud Keystores from the drop-down menu.
- Select the Cloud Keystore name that you want to perform a discovery on.
- From the pane that opens on the right of the screen, select Discovery configuration. Select the
 toggle switches to turn on "Enable scheduled discovery" and "Include expired certificates".
toggle switches to turn on "Enable scheduled discovery" and "Include expired certificates". - Under Repeat every, select your desired Daily, Weekly, or Advanced schedule. Then, choose your desired time.
- Click Save.